Boffins shows that sound output devices secretly capture audio
Computer speakers and headphones make passable microphones and can be used to receive data via ultrasound and send signals back, making the practice of air gapping sensitive computer systems less secure.
In an academic paper published on Friday through preprint service ArXiv, researchers from Israel’s Ben-Gurion University of the Negev describe a novel data exfiltration technique that allows the transmission and reception of data – in the form of inaudible ultrasonic sound waves – between two computers in the same room without microphones.
The paper, titled, “MOSQUITO: Covert Ultrasonic Transmissions between Two Air-Gapped Computers using Speaker-to-Speaker Communication,” was written by Mordechai Guri, Yosef Solwicz, Andrey Daidakulov and Yuval Elovici, who have developed a number other notable side-channel attack techniques.
These include: ODINI, a way to pass data between Faraday-caged computers using electrical fields; MAGNETO, a technique for passing data between air-gapped computers and smartphones via electrical fields; and FANSMITTER, a way to send acoustic data between air-gapped computers using fans.
Secret data transmissions of this sort expand on prior work done by National Security Agency on TEMPEST attacks, which utilize electromagnetic, magnetic, acoustic, optical and thermal emanations from electronic devices to collect and transmit data.
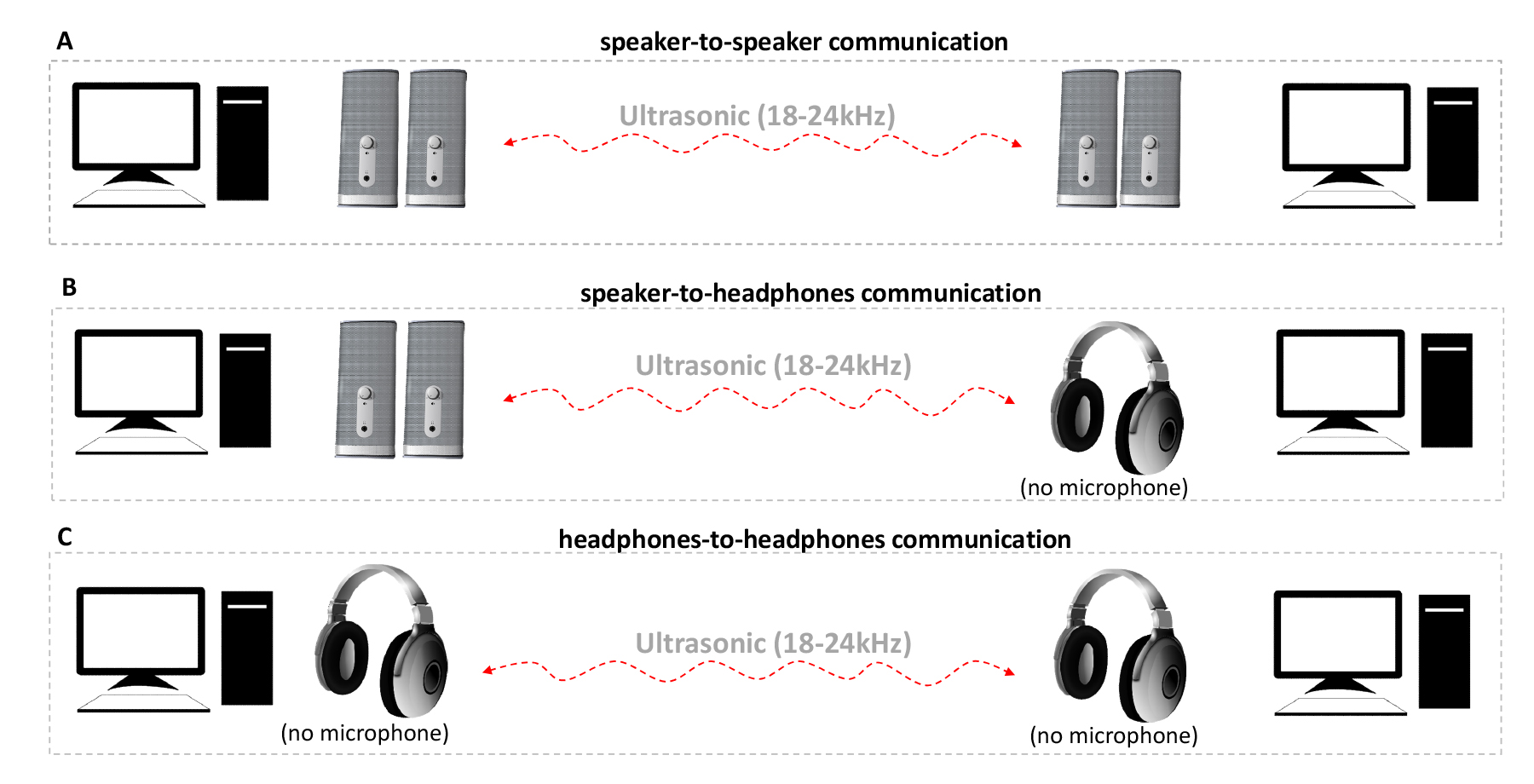
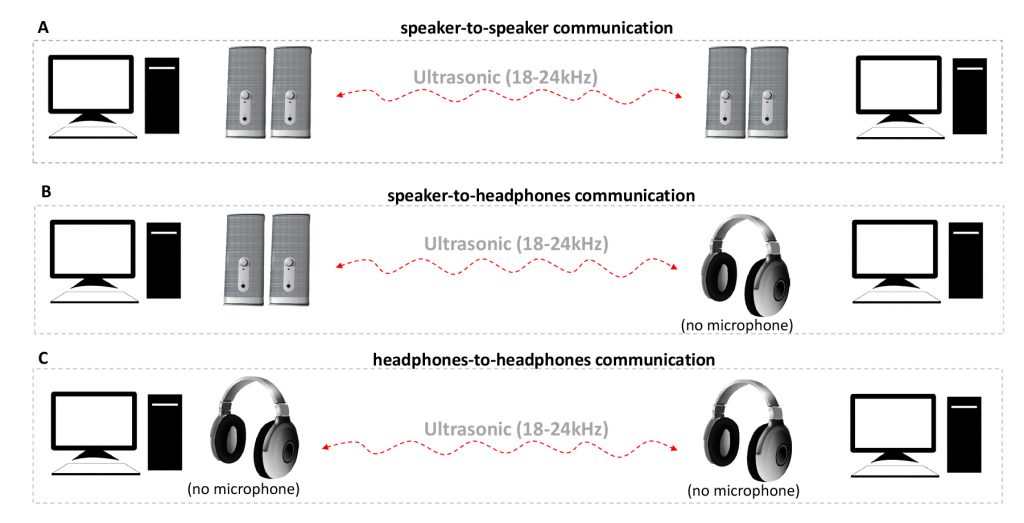
MOSQUITO, the researchers explain, demonstrates that speakers can covertly transmit data between unconnected machines at a distance of up to nine meters. What’s more, the technique works between mic-less headphones – the researchers say their work is the first to explore headphone-to-headphone covert communication.
Speakers, the paper explains, can be thought of as microphones working in reverse: Speakers turn electrical signals into acoustic signals while microphones turn acoustic signals into electrical ones. And each includes a diaphragm to assist with the conversion, which can help reverse the process.
Modern audio chipsets, such as those from Realtek, include an option to alter the function of the audio port via software, the paper explains. This capability is referred to as “jack retasking.”
“The fact that loudspeakers, headphones, earphones, and earbuds are physically built like microphones, coupled with the fact that an audio port’s role in the PC can be altered programmatically, changing it from output to input, creates a vulnerability which can be abused by attackers,” the paper explains.
Malware, thus, may be able to reconfigure a speaker or headphone to act as a microphone, provided the device is passive and unpowered.
That’s a significant caveat since most modern PCs have active, powered speakers; headphones and earbuds generally have passive speakers, as do some older PCs.
In an email to The Register, Mordechai Guri, one of the paper’s authors, head of R&D at Ben-Gurion University of the Negev’s Cyber-Security Research Center, and chief scientific officer at Morphisec, said, “The main problem involves headphones, earphones and earbuds since they are reversible and can become good pair of microphones (even when they don’t have an integrated mic at all).”
Using frequencies ranging from 18kHz to 24kHz, the researchers were able to achieve a data transmission rate of 166 bit/sec with a 1 per cent error rate when transmitting a 1Kb binary file over a distance of three meters. At distances ranging from 4 to 9 meters, that same error rate could only be achieved with a 10 bit/sec transmission rate, largely as a consequence of interference from environmental noise.
The paper discusses several mitigation techniques, all of which have limitations, including designing headphones and speakers with on-board amplifiers (which prevents use as a mic), using an ultrasonic jammer, scanning for ultrasonic transmissions, preventing jack retasking via software, and completely disabling audio hardware via the UEFI/BIOS.
Disconnecting speakers, headphones and the like represents the most practical solution, Guri said, “but this is not always feasible.”
Monitoring the ultrasonic band is a good theoretical and academic solution, he added, but has potential problems. “In practice, it will raise many false alarms,” he said.
Guri said ultrasonic malware does not appear to be very common. “A few years ago, a security researcher claimed that he found ultrasonic malware in the wild. It was dubbed BadBios. But in any case, it was claimed to be able to communicate between two laptops with both speakers and microphones.”
Inaudible audio is more likely to be used for marketing, and has prompted the development of defensive code called Silverdog. It’s an ultrasonic firewall in the Google Chrome browser that’s designed to block ultrasonic beacons (uBeacons), employed for cross-device tracking. ®
Source: TheRegister