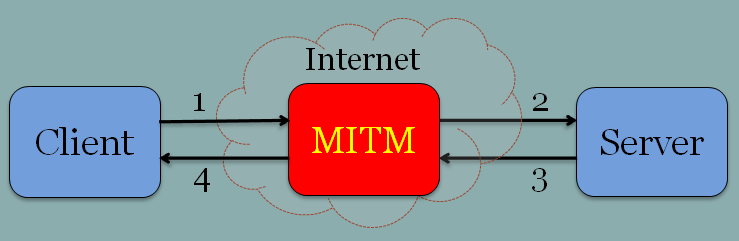
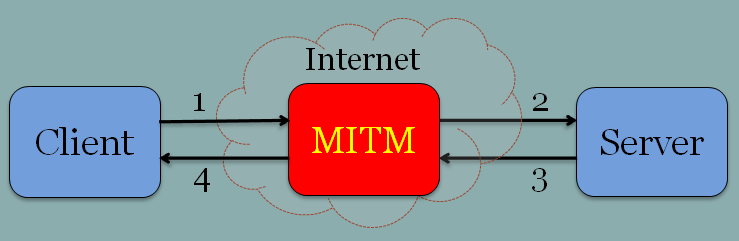
A man in the middle is a classic attack. If there was a popularity contest for attacks I would bet that MitM (Man-in-the-middle) would score one of the top three! To our readers who don’t know how it works then it is basically a setup of two endpoints that communicate with each other (i,e, client server) and someone or something seats somewhere in between and starts eavesdropping and maybe even changing the communications on the go.
Here is a nice illustration:
Still, I want to argue that not all MitMs are the same and although the name sounds the same their impact is not the same. By impact I mean the risk magnitude which can be calculated by how many people can be exposed to it and ease of deployment/propagation to another group of people.
Sounds tricky? No.
Let’s analyze few examples:
- A classic MitM is when someone hijacks a specific Wifi or pretending to be a legitimate wifi hotspot (usually being FREE is a good honeypot). In this case we can calculate the magnitude as: tens or maybe hundreds of users using the wifi multiplied by one. One wifi. Why one? Because you need to be in the specific place in order to create a wifi MitM and creating many MitMs on different Wifis is a hard work. Hackers don’t like to work hard. So we can rate the impact here is LOW.
- The second scenario is a virus which attacks let’s say internet Explorer (why not:) 6 on Windows XP and it propagates via mail. If we try to guesstimate the impact then let’s see: thousand of people got infected successfully where the propagation is actually tight together with the amount of victims so we can call it a MEDIUM-LOW magnitude. It can be much worse but I want to take the middle ground here. Apologies..
- The third scenario is an attack on a website server where the MitM eavesdrop unencrypted communications (let’s make it simple). Here the magnitude is calculated similarly to the Wifi scenario where the number of visitors of the site are multiplied by one in case of a single attack on a single site. Of course if the attack is on all Yahoo servers then it is big scale but since usually it is hard to propagate attacks like that among multiple servers then the impact stays usually at MEDIUM.
I could go on and on with other examples of different locations for an MitM but I guess you get the point.
So we have here different attacks on the three core areas in the composition of an MitM:
- The client side (as in the IE6 example)
- The middleware as in the Wifi
- The server side as in the third example
Where each part of the chain (and there can be more parts to the chain like the ISP and network devices in the middle) can pass through X amount of people – the first part of the magnitude equation. The other part of the equation is how easy it is to distribute the attack on this part of the chain and this becomes the number that is the multiplier of the first number (the X) which together are used to calculate in order to find out the risk magnitude.
Mobile phones present a new “opportunity” for MitM attacks to flourish. Why do I say this? Mobile security is a new industry and as such we see every other month a new product/tool/platform being launched and new protocols being adopted and companies created and collapsed. These volatility create the best conditions for finding new vulnerabilities which can serve all kind of attacks including MitM attacks. Now add to that an organized software distribution channel (app stores) where people in one click can install software and updates are running automatically and seamlessly so here you can have ease of propagation. Now add to that the fact that phones are being used more and more as the main computing tool which means more and more important stuff is going in and out of it. So if we try to create a magnitude calculation for an MitM attack which runs on the phone itself (inside the phone and not somewhere else) and propagates easily as a legitimate app and runs on a widely spread platform you get a CRITICAL risk.
I know it is not pure mathematics and there’s a lot of assumptions and guesses over here but for sure we can say that mobile phones with all the condition described earlier can raise MitM attacks to new heights in terms of risks.
Cyber Security Labs Team – Follow us via @cyberlabsbgu