THE FIELD OF cybersecurity is obsessed with preventing and detecting breaches, finding every possible strategy to keep hackers from infiltrating your digital inner sanctum. But Mordechai Guri has spent the last four years fixated instead on exfiltration: How spies pull information out once they’ve gotten in. Specifically, he focuses on stealing secrets sensitive enough to be stored on an air-gapped computer, one that’s disconnected from all networks and sometimes even shielded from radio waves. Which makes Guri something like an information escape artist.
More, perhaps, than any single researcher outside of a three-letter agency, Guri has uniquely fixated his career on defeating air gaps by using so-called “covert channels,” stealthy methods of transmitting data in ways that most security models don’t account for. As the director of the Cybersecurity Research Center at Israel’s Ben Gurion University, 38-year-old Guri’s team has invented one devious hack after another that takes advantage of the accidental and little-noticed emissions of a computer’s components—everything from light to sound to heat.
Guri and his fellow Ben-Gurion researchers have shown, for instance, that it’s possible to trick a fully offline computer into leaking data to another nearby device via the noise its internal fan generates, by changing air temperatures in patterns that the receiving computer can detect with thermal sensors, or even by blinking out a stream of information from a computer hard drive LED to the camera on a quadcopter drone hovering outside a nearby window. In new research published today, the Ben-Gurion team has even shown that they can pull data off a computer protected by not only an air gap, but also a Faraday cage designed to block all radio signals.
An Exfiltration Game
“Everyone was talking about breaking the air gap to get in, but no one was talking about getting the information out,” Guri says of his initial covert channel work, which he started at Ben-Gurion in 2014 as a PhD student. “That opened the gate to all this research, to break the paradigm that there’s a hermetic seal around air-gapped networks.”
Guri’s research, in fact, has focused almost exclusively on siphoning data out of those supposedly sealed environments. His work also typically makes the unorthodox assumption that an air-gapped target has already been infected with malware by, say, a USB drive, or other temporary connection used to occasionally update software on the air-gapped computer or feed it new data. Which isn’t necessarily too far a leap to make; that is, after all, how highly targeted malware like the NSA’s Stuxnet and Flamepenetrated air-gapped Iranian computers a decade ago, and how Russia’s “agent.btz” malware infected classified Pentagon networks around the same time.

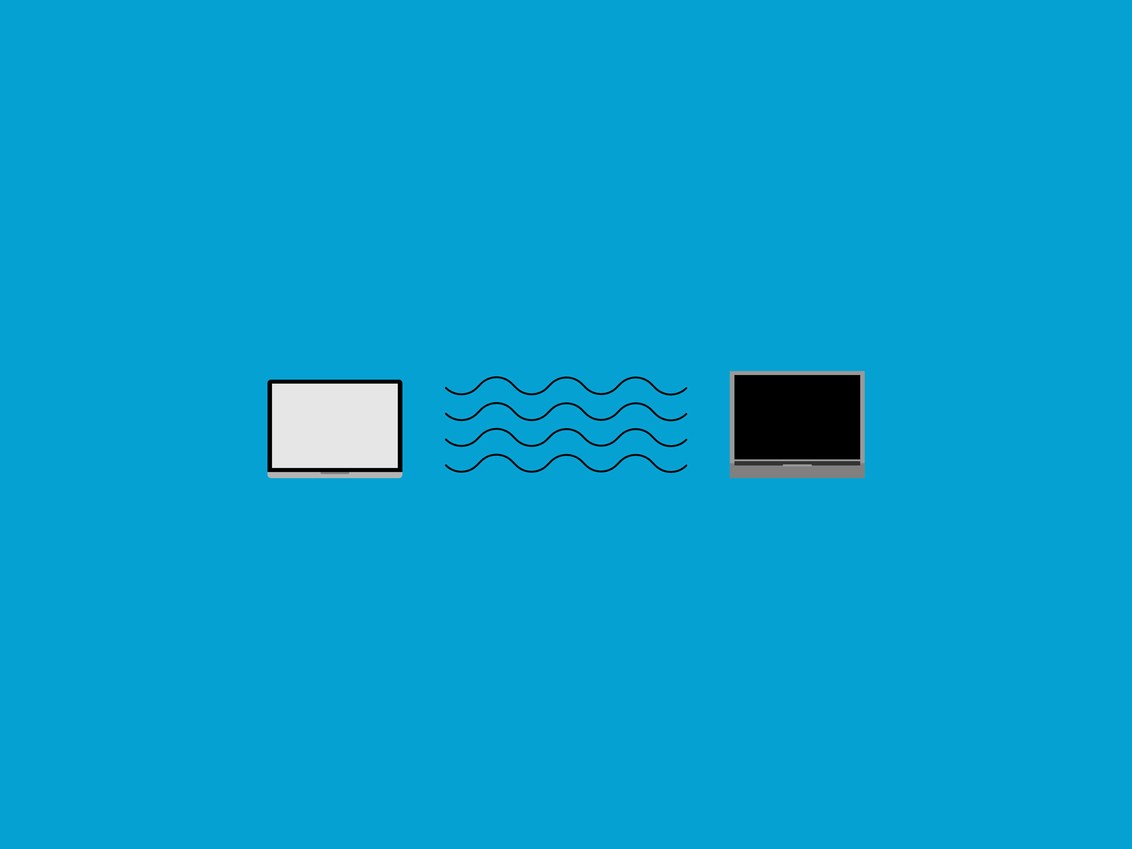
Guri’s work aims to show that once that infection has happened, hackers don’t necessarily need to wait for another traditional connection to exfiltrate stolen data. Instead, they can use more insidious means to leak information to nearby computers—often to malware on a nearby smartphone, or another infected computer on the other side of the air gap.
Guri’s team has “made a tour de force of demonstrating the myriad ways that malicious code deployed in a computer can manipulate physical environments to exfiltrate secrets,” says Eran Tromer, a research scientist at Columbia. Tromer notes, however, that the team often tests their techniques on consumer hardware that’s more vulnerable than stripped-down machines built for high security purposes. Still, they get impressive results. “Within this game, answering this question of whether you can form an effective air gap to prevent intentional exfiltration, they’ve made a resounding case for the negative.”
A Magnetic Houdini
On Wednesday, Guri’s Ben-Gurion team revealed a new technique they call MAGNETO, which Guri describes as the most dangerous yet of the dozen covert channels they’ve developed over the last four years. By carefully coordinating operations on a computer’s processor cores to create certain frequencies of electrical signals, their malware can electrically generate a pattern of magnetic forces powerful enough to carry a small stream of information to nearby devices.
The team went so far as to built an Android app they call ODINI, named for the escape artist Harry Houdini, to catch those signals using a phone’s magnetometer, the magnetic sensor that enables its compass and remains active even when the phone is in airplane mode. Depending on how close that smartphone “bug” is to the target air-gapped computer, the team could exfiltrate stolen data at between one and 40 bits a second—even at the slowest rate, fast enough to steal a password in a minute, or a 4096-bit encryption key in a little over an hour, as shown in the video below:
Plenty of other electromagnetic covert channel techniques have in the past used the radio signals generated by computers’ electromagnetism to spy on their operations—the NSA’s decades-old implementation of the technique, which the agency called Tempest, has even been declassified. But in theory, the radio signals on which those techniques depend would be blocked by the metal shielding of Faraday cages around computers, or even entire Faraday rooms used in some secure environments.
Guri’s technique, by contrast, communicates not via electromagnetically induced radio waves but with strong magnetic forces that can penetrate even those Faraday barriers, like metal-lined walls or a smartphone kept in a Faraday bag. “The simple solution to other techniques was simply to put the computer in a Faraday cage and all the signals are jailed,” Guri says. “We’ve shown it doesn’t work like that.”
Secret Messages, Drones, and Blinking Lights
For Guri, that Faraday-busting technique caps off an epic series of data heist tricks, some of which he describes as far more “exotic” than his latest. The Ben-Gurion team started, for instance, with a technique called AirHopper, which used a computer’s electromagnetism to transmit FM radio signals to a smartphone, a kind of modern update to the NSA’s Tempest technique. Next, they proved with a tool called BitWhisper that the heat generated by a piece of malware manipulating a computer’s processor can directly—if slowly—communicate data to adjacent, disconnected computers.
In 2016, his team switched to acoustic attacks, showing that they could use the noise generated by a hard drive’s spinning or a computer’s internal fan to send 15 to 20 bits a minute to a nearby smartphone. The fan attack, they show in the video below, works even when music is playing nearby:
More recently, Guri’s team began playing with light-based exfiltration. Last year, they published papers on using the LEDs of computers and routers to blink out Morse-code like messages, and even used the infrared LEDs on surveillance cameras to transmit messages that would be invisible to humans. In the video below, they show that LED-blinked message being captured by a drone outside a facility’s window. And compared to previous methods, that light-based transmission is relatively high bandwidth, sending a megabyte of data in a half an hour. If the exfiltrator is willing to blink the LED at a slightly slower rate, the malware can even send its signals with flashes so fast they’re undetectable for human eyes.
Guri says he remains so fixated on the specific challenge of air gap escapes in part because it involves thinking creatively about how the mechanics of every component of a computer can be turned into a secret beacon of communication. “It goes way beyond typical computer science: electrical engineering, physics, thermodynamics, acoustic science, optics,” he says. “It requires thinking ‘out of the box,’ literally.”
And the solution to the exfiltration techniques he and his team have demonstrated from so many angles? Some of his techniques can be blocked with simple measures, from more shielding to greater amounts of space between sensitive devices to mirrored windows that block peeping drones or other cameras from capturing LED signals. The same sensors in phones that can receive those sneaky data transmissions can also be used to detect them. And any radio-enabled device like a smartphone, Guri warns, should be kept as far as possible from air-gapped devices, even if those phones are carefully stored in a Faraday bag.
But Guri notes that some even more “exotic” and science fictional exfiltration methods may not be so easy to prevent in the future, particularly as the internet of things becomes more intertwined with our daily lives. What if, he speculates, it’s possible to squirrel away data in the memory of a pacemaker or insulin pump, using the radio connections those medical devices use for communications and updates? “You can’t tell someone with a pacemaker not to go to work,” Guri says.
An air gap, in other words, may be the best protection that the cybersecurity world can offer. But thanks to the work of hackers like Guri—some with less academic intentions—that space between our devices may never be entirely impermeable again.
Gap Attacks
- If you’re still not totally clear on what an air gap is, here’s a little explainer for you
- Yes, blinking LED lights on a computer really can leak data
- But they’ve got nothing on the fan noises that do the same
Source: Wired