Beware of smartphones and cameras around wallets storing your digital coin.
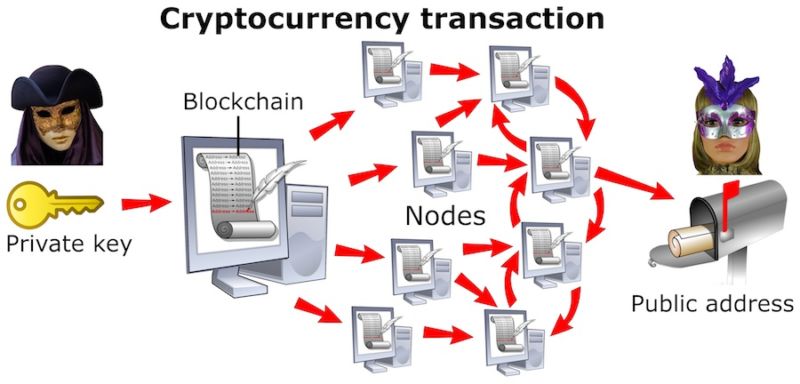
Researchers have defeated a key protection against cryptocurrency theft with a series of attacks that transmit private keys out of digital wallets that are physically separated from the Internet and other networks.
Like most of the other attacks developed by Ben-Gurion University professor Mordechai Guri and his colleagues, the currency wallet exploits start with the already significant assumption that a device has already been thoroughly compromised by malware. Still, the research is significant because it shows that even when devices are airgapped—meaning they aren’t connected to any other devices to prevent the leaking of highly sensitive data—attackers may still successfully exfiltrate the information. Past papers have defeated airgaps using a wide array of techniques, including electromagnetic emissions from USB devices, radio signals from a computer’s video card, infrared capabilities in surveillance cameras, and sounds produced by hard drives.
On Monday, Guri published a new paper that applies the same exfiltration techniques to “cold wallets,” which are not stored on devices connected to the Internet. The most effective techniques take only seconds to siphon a 256-bit Bitcoin key from a wallet running on an infected computer, even though the computer isn’t connected to any network. Guri said the possibility of stealing keys that protect millions or billions of dollars is likely to take the covert exfiltration techniques out of the nation-state hacking realm they currently inhabit and possibly bring them into the mainstream.
“I think that the interesting issue is that the airgap attacks that were thought to be exotic issues for high-end attacks may become more widespread,” he wrote in an email. “While airgap covert channels might be considered somewhat slow for other types of information, they are very relevant for such brief amounts of information. I want to show the security of ‘cold wallet’ is not hermetic given the existing airgap covert channels.”
One technique can siphon private keys stored in a cold wallet running on a Raspberry Pi, which many security professionals say is one of the best ways to store private cryptocurrency keys. Even if the device became infected, the thinking goes, there’s no way for attackers to obtain the private keys because it remains physically isolated from the Internet or other devices. In such cases, users authorize a digital payment in the cold wallet and then use a USB stick or other external media to transfer a file to an online wallet. As the following video demonstrates, it takes only a few seconds for a nearby smartphone under the attacker’s control to covertly receive the secret key.
The technique works by using the Raspberry Pi’s general-purpose input/output pins to generate radio signals that transmit the key information. The headphones on the receiving smartphone act as an antenna to improve the radio-frequency signal quality, but in many cases they’re not necessary.
A second video defeats a cold wallet running on a computer. It transmits the key by using inaudible, ultrasonic signals. Such inaudible sounds are already being used to covertly track smartphone users as they move about cities. It wouldn’t be a stretch to see similar capabilities built into malware that’s designed to steal digital coins.
As already mentioned, the exfiltration techniques described in this post assume the device running the cold wallet is already infected by malware. Still, the widely repeated advice to use cold wallets is designed to protect people against this very scenario.
“We show that, despite the high degree of isolation of cold wallets, motivated attackers can steal the private keys out of the air-gapped wallets,” Guri wrote in the new paper. “With the private keys in hand, an attacker virtually owns all of the currency in the wallet.”
To protect keys, people should continue to store them in cold wallets whenever possible, but they should consider additional safeguards, including keeping cold wallets away from smartphones, cameras, and other receivers. They should also shield cold-wallet devices with metallic materials that prevent electromagnetic radiation from leaking. Of course, people should also prevent devices from becoming infected in the first place.
Source: Ars Technica