CBG in the News
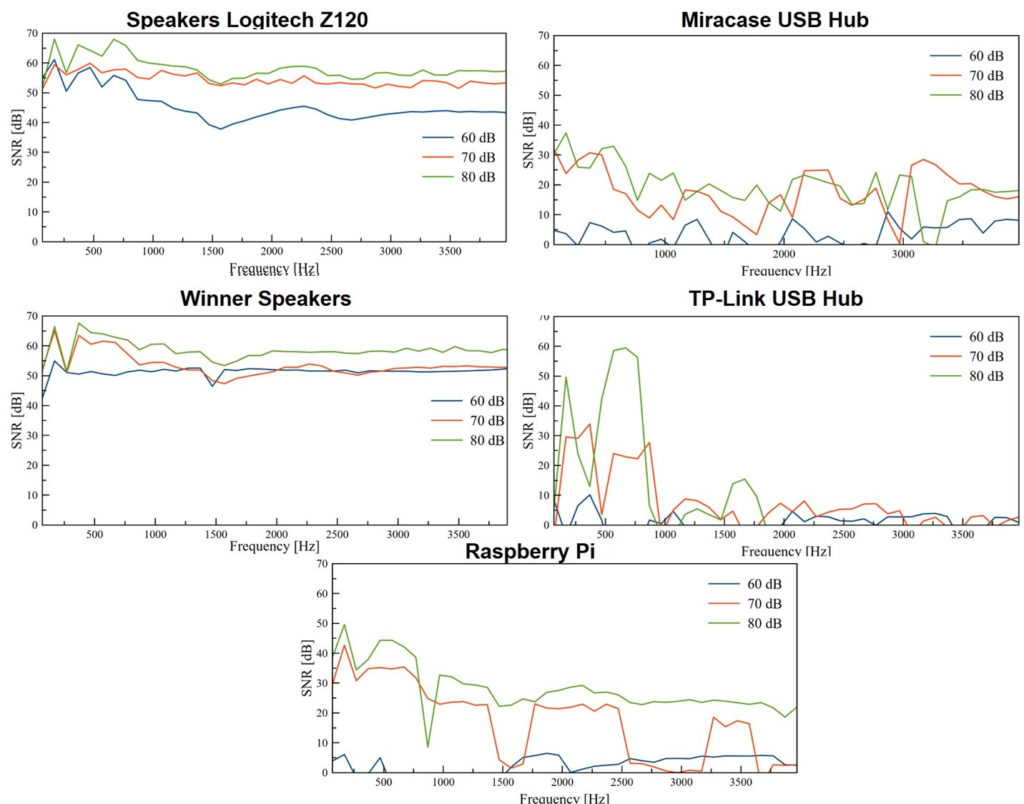
New “Glowworm attack” recovers audio from devices’ power LEDs
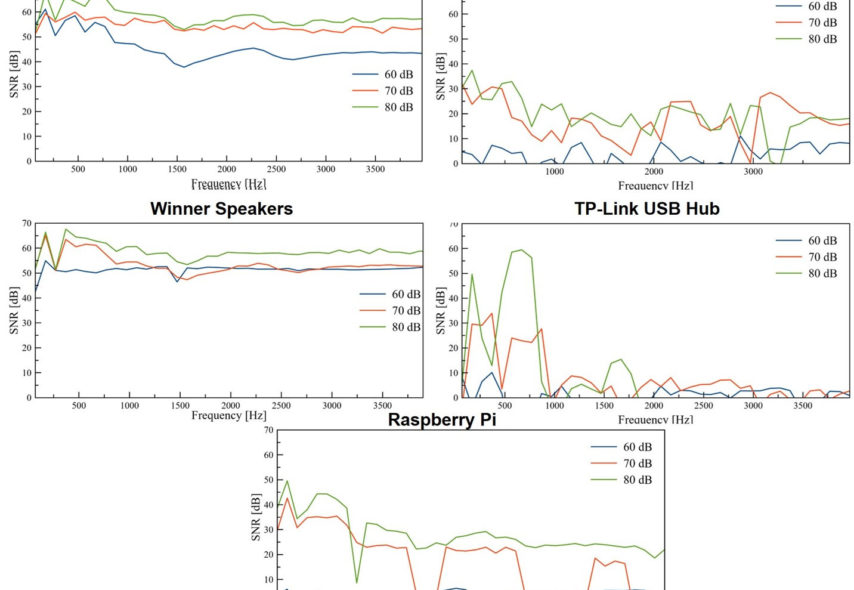
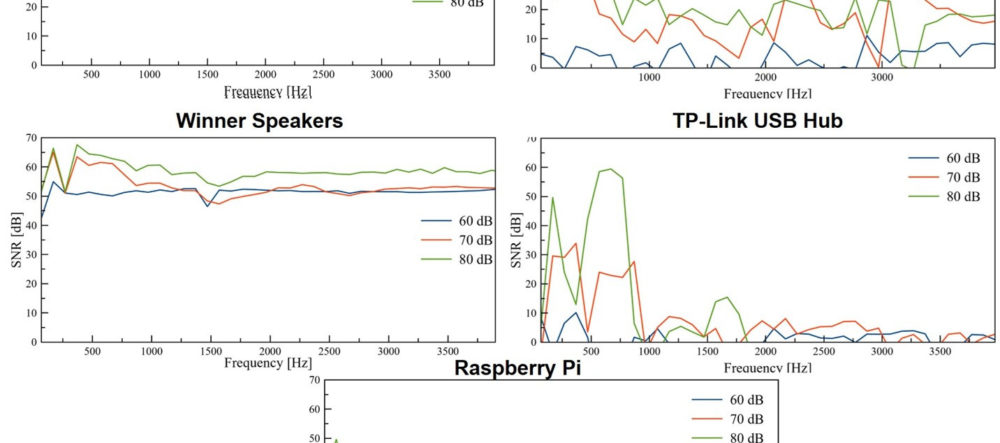
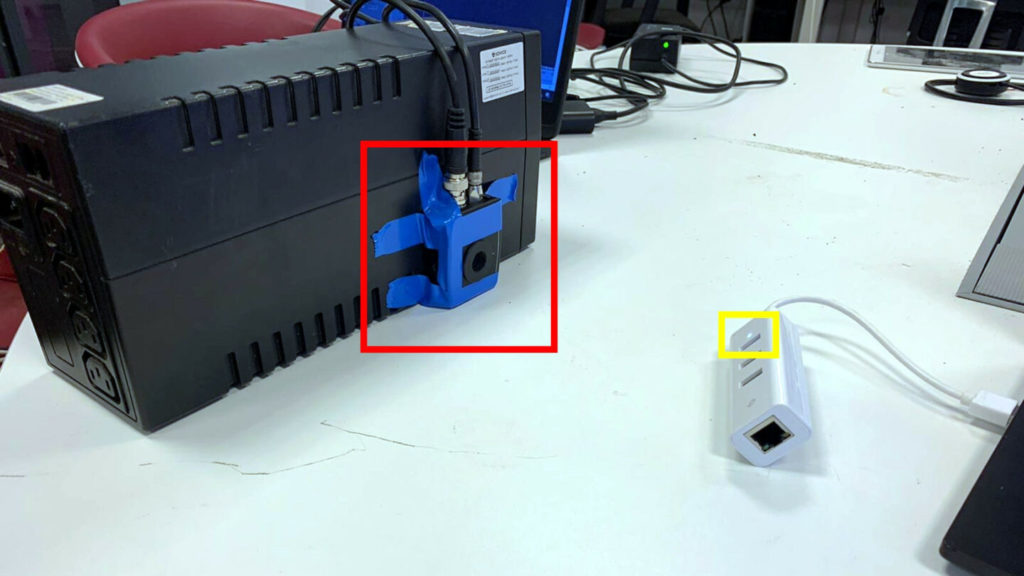
A new class of passive TEMPEST attack converts LED output into intelligible audio. Researchers at Ben-Gurion University of the Negev have demonstrated a novel way to spy on electronic conversations. A new paper released today outlines a novel passive form of the TEMPEST attack called Glowworm, which converts minute fluctuations in the intensity of power LEDs on speakers and USB hubs back into the audio signals that caused those fluctuations. The Cyber@BGU team—consisting of Ben Nassi, Yaron Pirutin, Tomer Gator, Boris Zadov, and Professor Yuval Elovici—analyzed a broad array of widely used consumer devices in...
Read More ...U.S.-Israel Energy Center announces winner of $6m funding for cybersecurity solutions in energy sector
The selected consortium, which included a number of American and Israeli companies and universities, will receive a total of $6 mi...
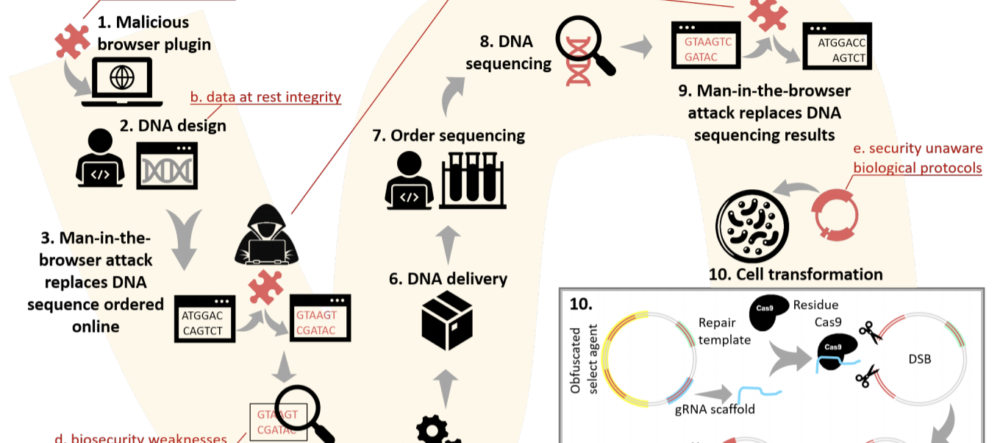
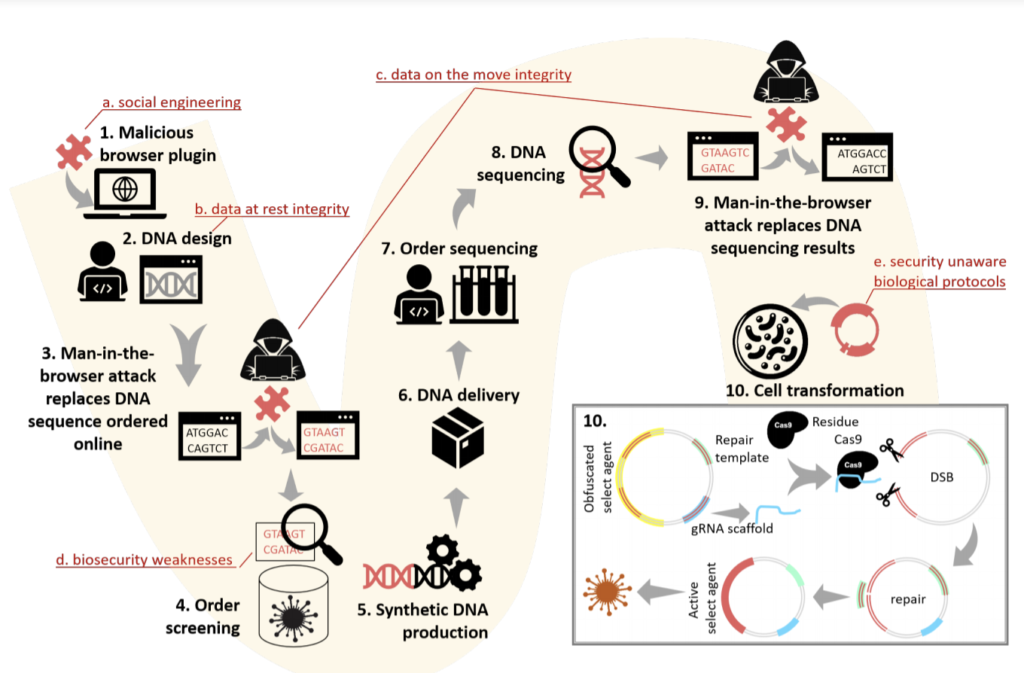
Read More ...This new cyberattack can dupe DNA scientists into creating dangerous viruses and toxins
The research highlights the potential dangers of new ‘biohacking’ techniques. A new form of cyberattack has been devel...
Read More ...Split-Second ‘Phantom’ Images Can Fool Tesla’s Autopilot
Researchers found they could stop a Tesla by flashing a few frames of a stop sign for less than half a second on an internet-conne...
Read More ...BGU researchers find it’s easy to get personal data from Zoom screenshots
Scientists warn that users should not post screen images of their video conference sessions on social media Personal data can easi...
Read More ...Spies Can Eavesdrop by Watching a Light Bulb’s Vibrations
The so-called lamphone technique allows for real-time listening in on a room that’s hundreds of feet away. THE LIST OF&nbs...
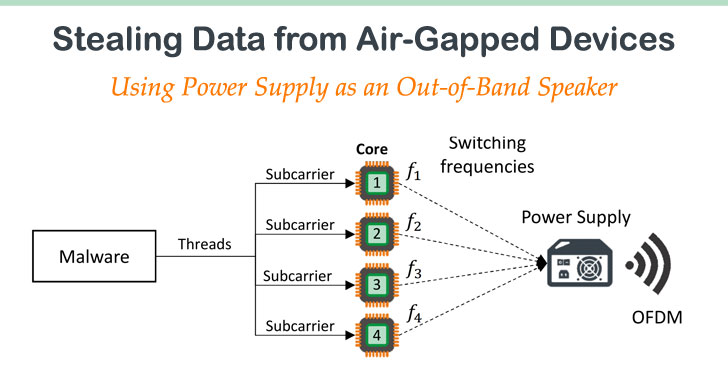
Read More ...New Malware Jumps Air-Gapped Devices by Turning Power-Supplies into Speakers
Cybersecurity researcher Mordechai Guri from Israel’s Ben Gurion University of the Negev recently demonstrated a new kind of...
Read More ...Israel Warns: Hackers Can Threaten Getting CoronaVirus Under Control
For they assailed you by the trickery they practiced against you because of the affair of Peor and because of the affair of thei...
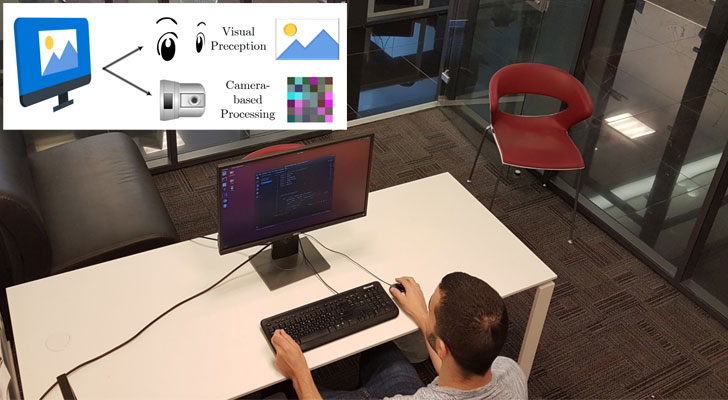
Read More ...Exfiltrating Data from Air-Gapped Computers Using Screen Brightness
It may sound creepy and unreal, but hackers can also exfiltrate sensitive data from your computer by simply changing the brightnes...
Read More ...How a $300 projector can fool Tesla’s Autopilot
Semi-autonomous driving systems don’t understand projected images. Six months ago, Ben Nassi, a PhD student at Ben-Guri...
Read More ...Actuator Power Signatures Defend Against Additive Manufacturing Sabotage Attacks
Researchers have come together from the US and Israel to study potential threats that could affect additive manufacturing systems....
Read More ...Did you really ‘like’ that? How Chameleon attacks spring in Facebook, Twitter, LinkedIn
Social networks impacted seem to disagree on the scope of the attack. Social networks are full to the brim with our photos, posts,...
Read More ...