Our Professional and Humble Response to Samsung
Three weeks ago on the 23rd of December 2013, a story was published in the Wall Street Journal (WSJ) regarding a vulnerability we uncovered on Samsung KNOX devices. We’ll begin with a little background about the vulnerability. We found that a malicious app (without ROOT) running in the non-secure area of a KNOX based device (for example, […]
We’ve Got A Twitter Address – @cyberlabsbgu

We’ve got a new twitter address where you can track our discoveries and other posts on cyber security. Here it is @cyberlabsbgu.]
In an Unintended Way or The Morale Attacker

Recently Samsung published a statement about a vulnerability we uncovered and although we will respond on that later with more details, still one sentence captured my curiousity and that is: “… the exploit uses legitimate Android network functions in an unintended way to intercept …”. It seems like someone is applying moral judgement to the way the exploit works. It […]
VPN Related Vulnerability Discovered on an Android device – Disclosure Report

As part of our ongoing mobile security research we have uncovered a network vulnerability on Android devices which has serious implications for users using VPN. This vulnerability enables malicious apps to bypass active VPN configuration (no ROOT permissions required) and redirect secure data communications to a different network address. These communications are captured in CLEAR […]
Man in the middle attack – not all are created equal!
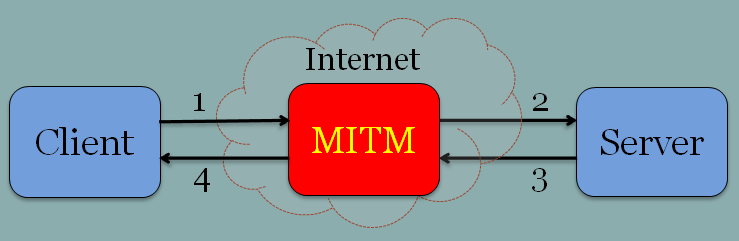
A man in the middle is a classic attack. If there was a popularity contest for attacks I would bet that MitM (Man-in-the-middle) would score one of the top three! To our readers who don’t know how it works then it is basically a setup of two endpoints that communicate with each other (i,e, client server) […]
About Us in Pictures
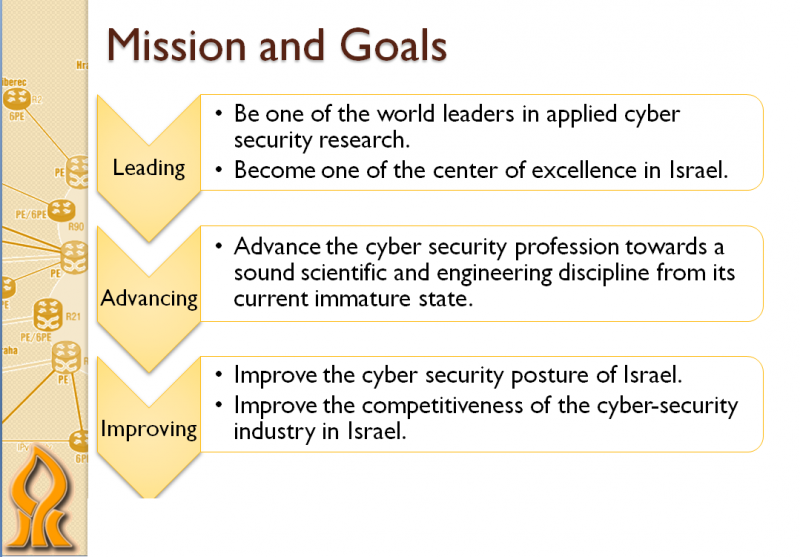
The Cyber Security Research Center @ Ben-Gurion University is a new institution and such we are in the phase of defining our goals, core competences and performance indicators. Our Goals Our Core Competences Our Performance Indicators So we have lot’s of work ahead of us:)
Our Disclosure Policy – A Responsible One!

During our work we naturally encounter vulnerabilities and security related issues which present an immediate risk to specific organizations and/or the public. Deciding what to do with a vulnerability is not an easy decision since from the moment you know about it in a way you share the responsibility on might happen to the people […]
Cyber Labs in the News

Recent news coverage: Samsung Phone Studied for Possible Security Gap / WSJIsraeli Researchers Point to Alleged Vulnerability in Galaxy S4 Samsung: Knox Security Gap Not Specific to Galaxy Devices / WSJ Digits Android VPN flaw found, exposes protected data / ZDNet Israeli Android researchers demo VPN vulnerability / The Register Android flaw allows attackers to bypass VPN, capture unencrypted […]
Cybertech – Cyber Security Conference – Israel 2014

Israel Defense, Prime Minister’s Office National Cyber Bureau, Kenes Exhibitions, and Ben-Gurion University of the Negev are pleased to invite you to the International Exhibition & Conference for Cyber Solutions, which will bring together leading multi-national companies, over a hundred start-ups, private and corporate investors, venture capital firms, experts, clients and many more. The event will […]
Welcome To The Blog of The Cyber Security Labs of Ben Gurion University of the Negev in Israel
Welcome to our new shiny blog! The cyber security labs of Ben Gurion university is located in Beer Sheva, the capital of the Negev which is the southern part of Israel and it was founded three months ago. Just to be clear, starting 3 months ago does not mean we are newbies. We are a large team of […]
Researchers discover vulnerability in Samsung’s Knox BYOD software

A security vulnerability within the Knox software used by the Samsung Galaxy S4 and the Note 3 could allow a malicious app to “listen in” on data transferred within the secured environment, researchers warned. On Jan. 9, Samsung dismissed the findings as a “man in the middle attack”. The vulnerability was reported Tuesday by The […]
CoBAn: A context based model for data leakage prevention
In collaboration with Telekom Innovation Laboratories G Katz, Y Elovici, B Shapira Information sciences 262, 137-158, 2014 Link to document A new context-based model (CoBAn) for accidental and intentional data leakage prevention (DLP) is proposed. Existing methods attempt to prevent data leakage by either looking for specific keywords and phrases or by using various statistical […]
