New research from Ben-Gurion University of the Negev in Israel, that previously showed how easy it is to hack 3D printed drones, is proposing the use of “audio fingerprints” to help 3D printing avoid cyber-attacks.
The team’s research is valuable to concerns surrounding the security of 3D printing– a discussion that has tremendous value in industrial additive manufacturing sectors such as aerospace, automotive and defense.

How does that sound?
To start the Ben-Gurion University study, researchers explain “that in FDM technology, the geometry of a printed object is defined by the movements of four stepper motors,” – three for X/Y/Z axes and one for filament extrusion. When 3D printing, these stepper motors generate a unique sound which is directly related to the specifics of the 3D modeled object, i.e. small features/layers yield short, high pitched noises, longer layers create a more prolonged sound.

As such, a perfect version of an object as it is 3D printing will emit a very specific sound. An imperfect version with, for example, internally embedded gaps or voids will sound different.
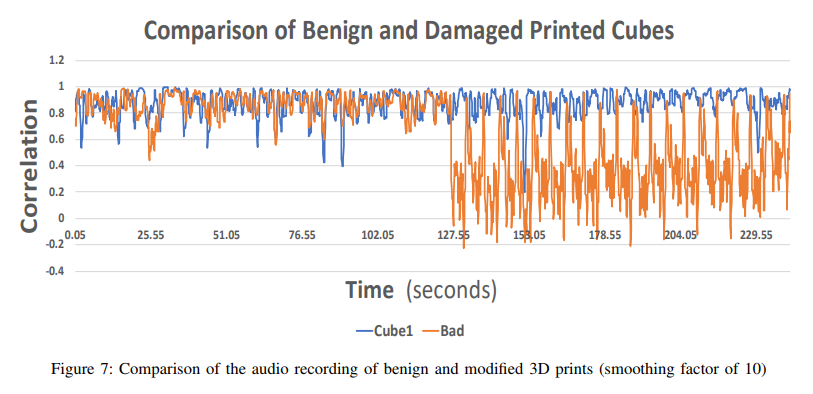
The Ben-Gurion University team’s idea is to record the sound of a perfect, 3D printed object, and use this as a “master audio fingerprint.” Each time the same object is 3D printed, the sounds of the stepper motors are recorded, and this is compared real-time to the master file to ensure it matches up.
Great variation between the wave pattern of the audio files therefore signifies a potential flaw in its structure. Once detected, prints are stopped in progress saving time and material waste.
“Highly efficient in detecting cyber-physical attacks”
By using this method, the team have successfully detected 6 potential sabotage attacks of 3D printed parts, including voids, different layer thickness, scale of the 3D printed object, X, Y or Z orientation changes, and fill pattern modification.
The amount of extruded filament however, and a temperature difference, are not detectable by audio fingerprint – though these prints are likely to fail from the offset anyway.
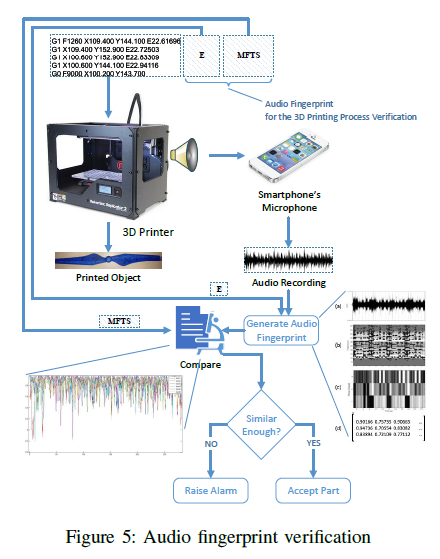
Conclusions state that “the proposed detection method is highly efficient in detecting cyber-physical attacks that aim to modify the object’s geometry or the printing process timing.”
The full results of this study, titled “Digital Audio Signature for 3D Printing Integrity“, are published, open access, in IEEE Transactions on Information Forensics and Security journal. The paper is co-authored by Sofia Belikovetsky, Yosef Solewicz, Mark Yampolskiy, Jinghui Toh and Yuval Elovici.
Source: 3D Printing Industry